Why is it important to verify who sent the email before you open or click on an email?
Hackers prey upon thoughtless human error. They count on their recipients to react before they think. To stay ahead, it’s important to arm yourself with knowledge and keep your common sense at the forefront when using your work email. One of the easiest ways to prevent problems is to verify who sent the email you’re receiving.
How to Verify Email Senders
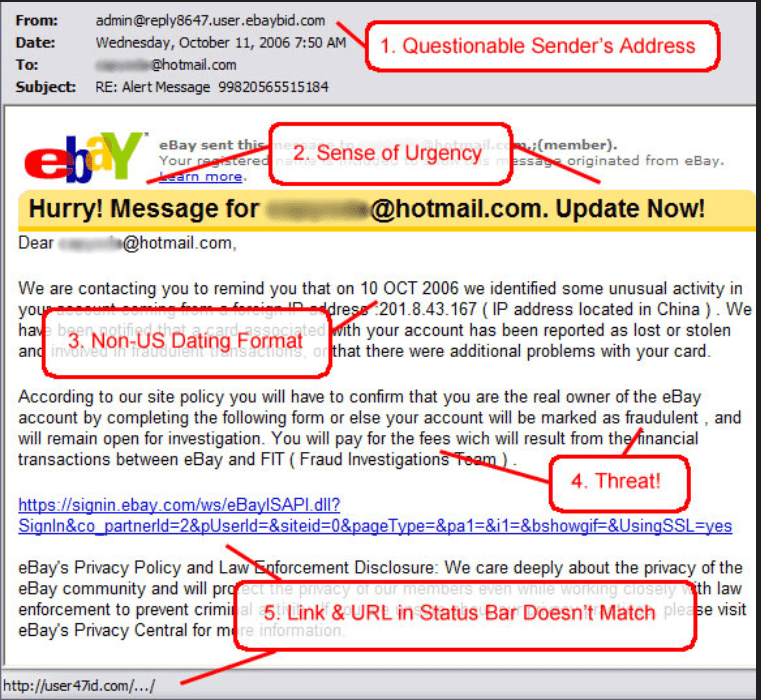
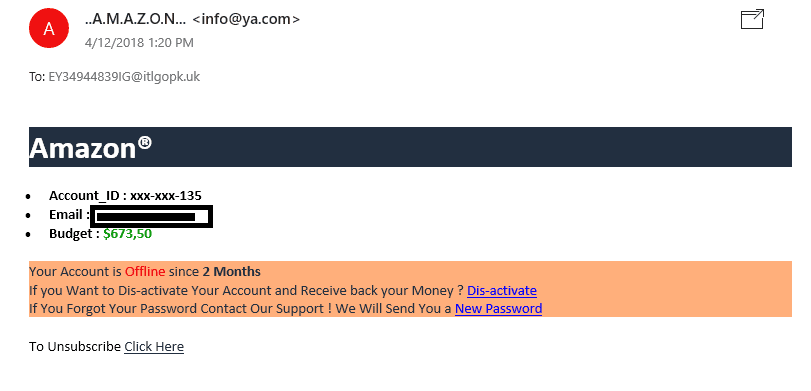
When you get an email, notice the name in the From line. Often, hackers will slide slight variations in here that are easily scanned over at a quick glance. Putting the letters R and N together in lowercase form can be mistaken for a lower case m (rn) if you’re not paying close attention.
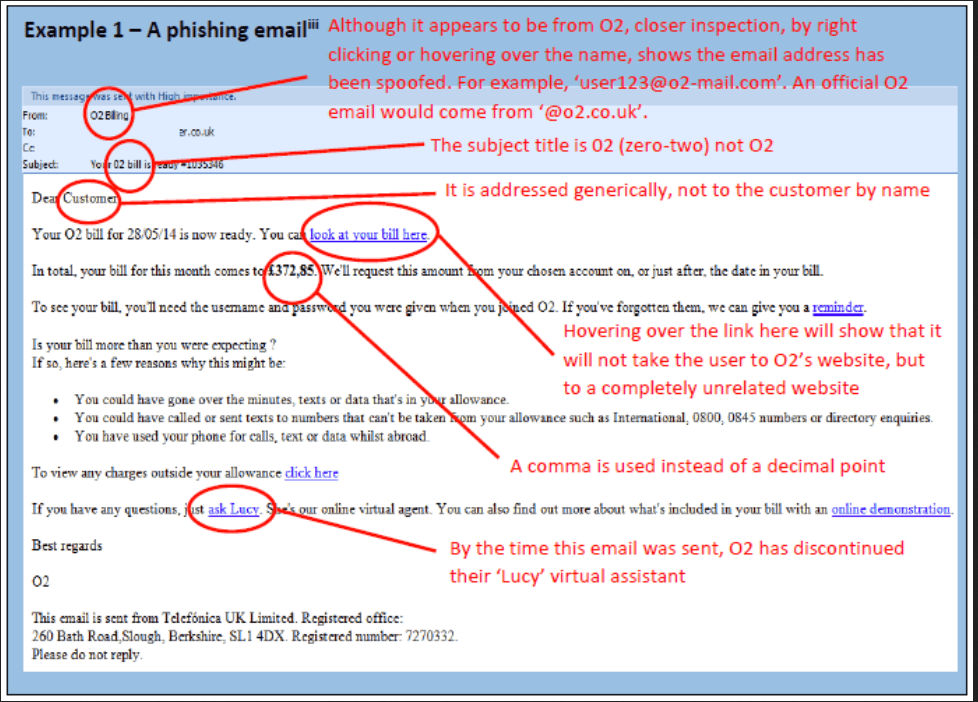
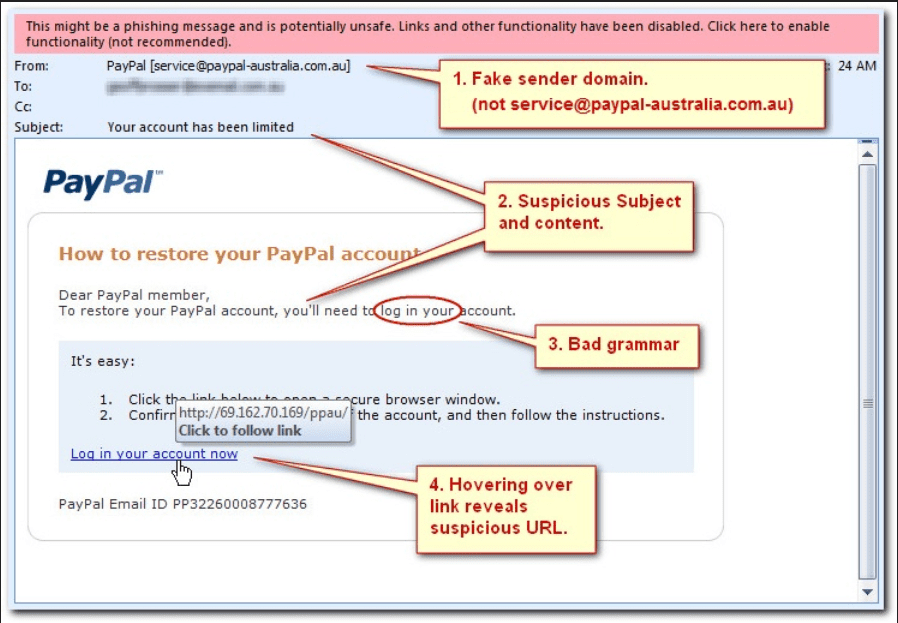
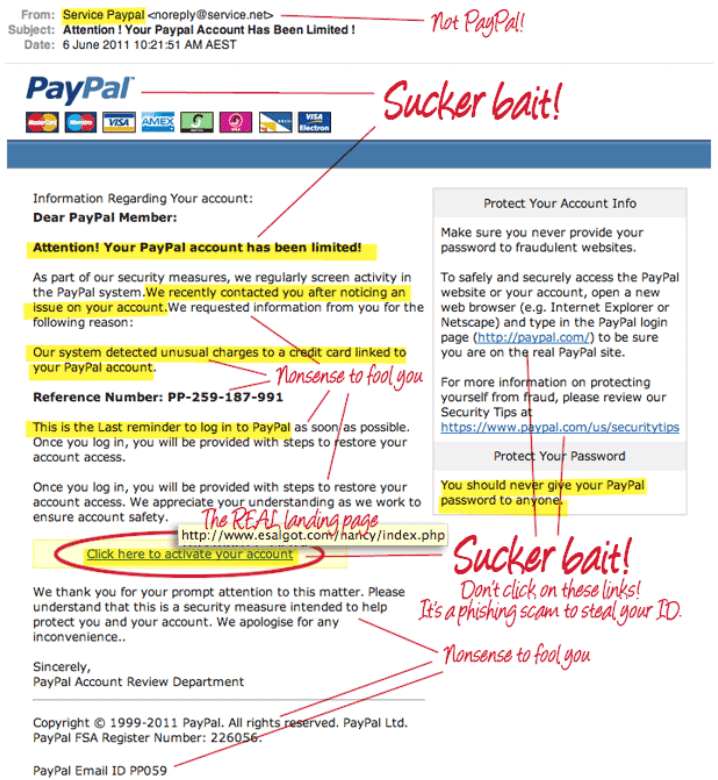
Once you’ve thoroughly examined the From field, the next step is to check the email address attached to it, which will likely be in brackets [abc@123.com]. Many times, the email address is different from the display name by a remarkable amount, and other times, the variations are more subtle. Check for extra letters (an extra o in Google [Gooogle], etc.) This is referred to as spoofing or phishing.
A good way to verify what an email address should be is to open a new browser tab, type in the company name, and navigate to the Contact Us page. For example, the return email on the MobileMe scam says it’s no-reply@m-e.com.
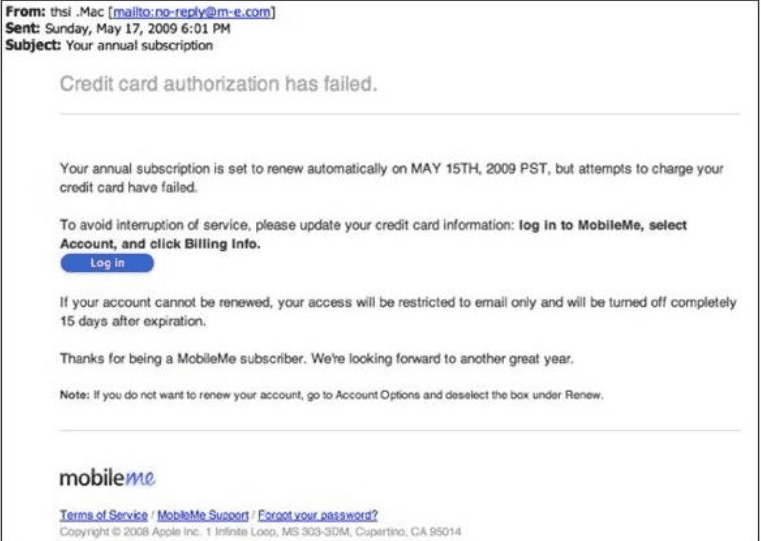
But when you Google MobileMe, you’ll notice it’s a service provided by Apple that no longer exists. Further research shows that the web address used to be me.com, but the email scam says m-e.com. These subtle changes are what often fool people into believing an email is legitimate when it’s not, leading to malware, spyware, ransomware, or surrendering money to a scammer.
Don’t Click That Hyperlink!
Many people click links that lead to harmful websites or open virus downloads because they don’t realize they can view the link destination in an email simply by hovering over it. This action displays the link destination, which is often not the site address you would expect to be associated with the information in the email.
If ever something seems amiss, it’s wise to contact your IT department before taking any other action. A good IT provider should have a method in place for assessing the safety of an email (things like being able to check links in a designated safe place). Better to verify and find out everything is okay than to infect your computer and give hackers access to your work network.
This method also works on buttons (think unsubscribe or sign in).
Sudden Prompts
Another tactic is the scare method.
“Your payment was declined!” “Your account has been frozen!” “Your password needs to be changed!”
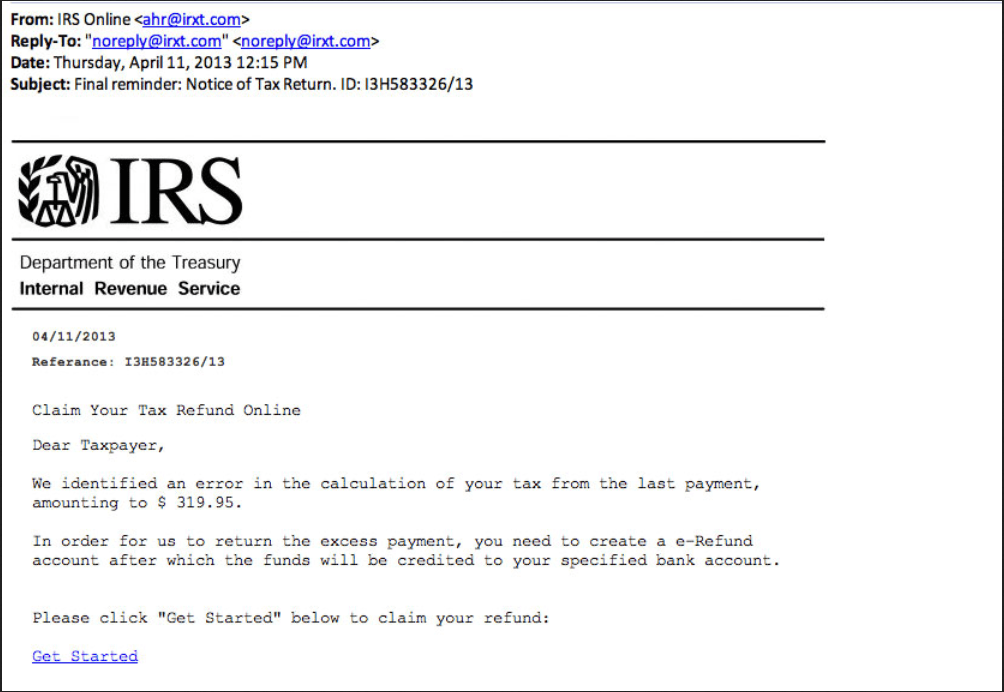
All of these tactics are designed to prey on your alarm response. “Oh no!” you think. Before you pause to question, you’ve clicked the link to rectify the issue and… virus. Watch for sudden prompts to change passwords and requests for personal information. Often, these are not legitimate. If you’re unsure, you can always call customer service to verify the validity of the claims in the email.
The Scam Is In the Details
Look closely. Often, spammers will swap letters for numbers (the letter O for the number 0), use the wrong punctuation (a comma instead of a decimal point or period), and use general titles (customer instead of name, Ms. instead of name, etc.). Grammar will likely be slightly wonky, like someone is trying to use English who doesn’t fully understand it (the wrong tense or spelling of a word). Other times, hackers will attach extra things to the end of a seemingly legitimate address (like a number or an extra letter).
Scan Your Business
In 2019, “66% of SMBs reported being the victim of a cyberattack and 63% reported a data breach.” Check out our 2019 Risk Report to view data of actual vulnerabilities that we found in several businesses that could have contributed to the numbers of that statistic. In the digital age of business, it’s important to know where you have gaps in your cybersecurity.

Utilize Your IT Team
Recognizing emails as bogus won’t always work; sometimes entire systems get hacked, like the bomb threats email chain, and the sender email is legitimate. In cases like that, you’ll want to contact your IT team before doing anything. If you don’t have the resources in-house, considering outsourcing to an IT team that places great importance on cybersecurity. Check out our article on the 5 questions to ask your IT provider to help your business find the best service.
Many hackers prey upon your immediate reaction – how people tend to do before they think. Pause, take a deep breath, walk away from the computer, and give yourself time to process so you can rationally and logically respond to the situation at hand.
Traveling for business? Stay safe on the go with our Electronic Safety Checklist for Business Travel.
Subscribe to our blog